Objective:
Find the password to the next level
Intel Given:
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
How to:
Our intel seems pretty straightforward for this level. There’s a script in cron, the script scheduler that let’s users and programs create and select scripts and programs to execute at a certain time, that contains the password. Cron can be used to schedule things to run daily, weekly, monthly, or hourly. It is a powerful tool to automatically set up backups, download and install updates, and anything else that needs to be run at a certain time. Our intel suggests that we should look in the cron directory so let’s take a look.
cronjob_bandit22 looks promising so let’s open it up. Cron’s format is a little unorthodox so let’s take a look. there are 5 spaces for specifying what time to run the script or program. If the space isn’t needed a star is used as a placeholder. The first position is used to denote , the minute using a value between 0-59. The second one is hour, using the 24 hour clock, meaning values between 0-23. The third place is used for day of the month, using values ranging from 1-31. The fourth space is month, specified by numbers between 1-12. The fifth position is used for day of the week, depending on the distribution 0 or 7 could be Sunday, I recommend checking on any distribution that you’re not sure about. The next part of a cron job is the username that executes the job. The final part of the cron job command is the script or program that is to be executed.
If you’re having trouble visualizing this here’s a graphic from adminschoice.com
* * * * * command to be executed
– – – – –
| | | | |
| | | | +—– day of week (0 – 6) (Sunday=0)
| | | +——- month (1 – 12)
| | +——— day of month (1 – 31)
| +———– hour (0 – 23)
+————- min (0 – 59)
There’s also a tool for showing what a proper cron configuration should look like for whatever you would like at corntab.com http://www.corntab.com/pages/crontab-gui. Edit: User Christian has emailed us and told of us another cool alternative http://crontab.guru/
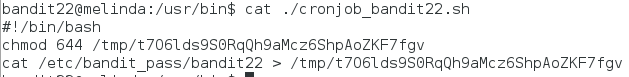
Now that we know the basics of cron let’s take a look at the script we have at hand.
Looks like this script is set to run every minute of every hour of every day of the month of every month and every day of the week. If this had been a resource intense one like a backup across a network it could cause some serious problems. I have a feeling, however that it is pretty small and doesn’t take up a lot of resources. So to further investigate let’s see what the script does.
looks like this script changes the file permissions of a file in the /tmp/ directory to enable the read and write permission for the user, and read permission for the group and everyone else. The /tmp directory is similar to the temp file folder in Windows, it’s used to create random directory and file names for use in programs and scripts. The second line in the script looks like it reads the file bandit22 in the /etc/bandit_pass/ directory and then uses the greater than sign (>). In Linux this is used to write text from one file to another, so the file bandit22 is essentially being copied to the /tmp/t7O6lds9S0RqQh9aMcz6ShpAoZKF7fgv file. If we wanted to write more than one file to a file we would have to add another of the brackets like so >>, this tells the shell that instead of writing over the file to add them to the bottom of the file. This technique is mostly used to write outputs to logs that otherwise would go to the standard output. Anyway let’s find that password.
The script wrote it to the file in the /tmp/ directory so let’s try to cat it.
Alright looks good!
Conclusion:
We learned about how cron works, a little bit about scripts, and how to write files using cat.